In the ever-evolving landscape of digital experiences, devices play a crucial role in shaping user interactions and data access. This article explores the dynamic relationship between devices, data, and digital experiences, highlighting their profound impact on the digital landscape. From providing structural support to ensuring data integrity, understanding the role of devices in digital experience foundations is essential for optimizing the overall user journey.
The fusion of devices, data, and digital experiences has transformed how businesses engage with their stakeholders. With the widespread adoption of smartphones, tablets, laptops, and other internet-enabled devices, users now have unprecedented access to various digital services and applications. This transformative change has led to a new era of personalized and seamless interactions, enabling businesses to deliver enhanced user experiences and achieve greater customer satisfaction.
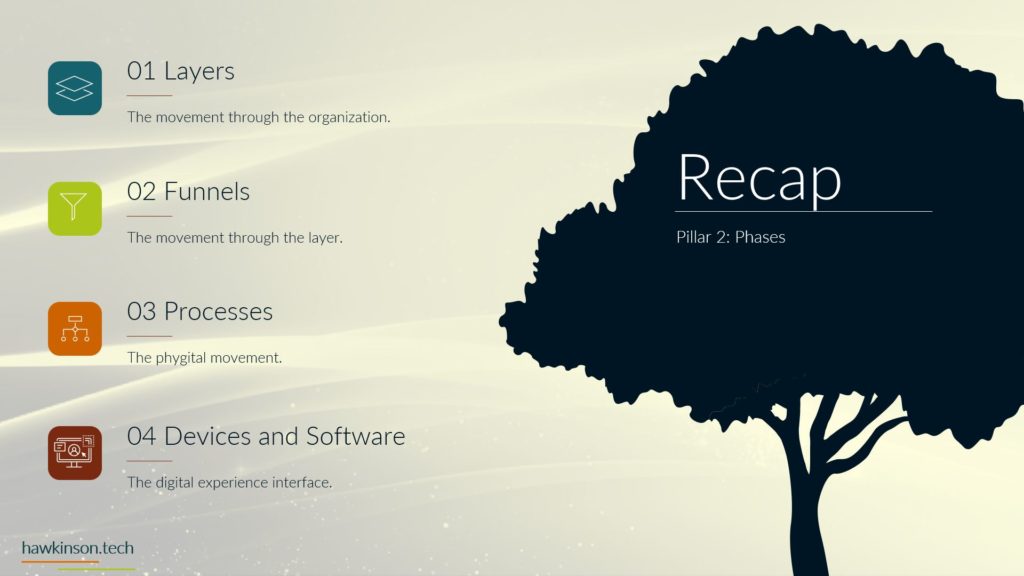
Devices as Architectural Pillars
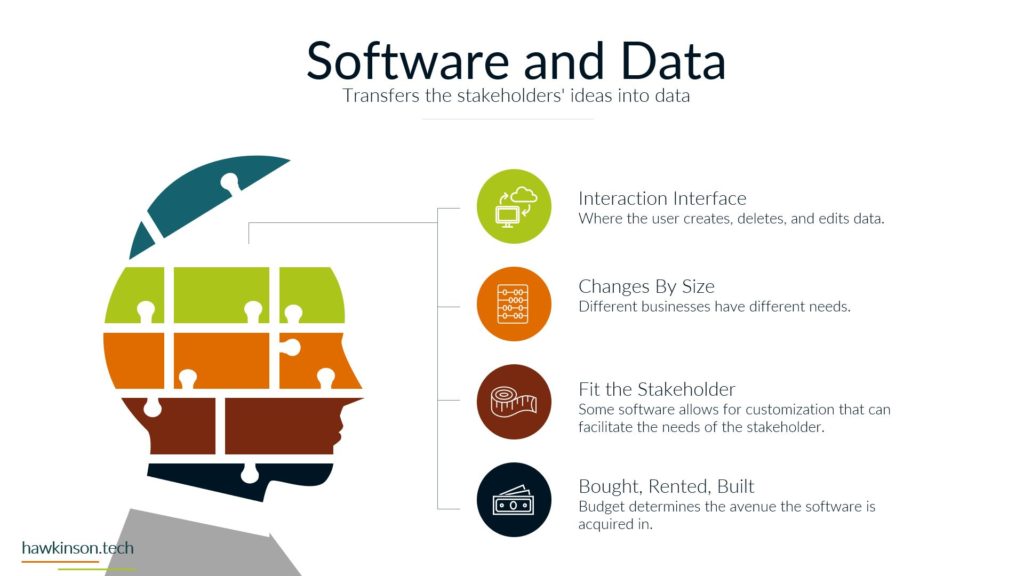
Devices form the bedrock of the digital experience, acting as a bridge between stakeholders and software interfaces. As software serves as an interface, devices bestow structure upon the digital journey, rendering software usable and purposeful. By enabling access to software, devices unlock their full potential. This section delves into the symbiotic relationship between devices and data, exploring how devices enhance software usability and user experience.
The Role of Devices in Digital Experiences
In the digital age, devices are the primary conduit for users to access and interact with digital content. They are the gateway to a vast virtual world where information, services, and entertainment are just a few taps or clicks away. With their intuitive interfaces and powerful processing capabilities, devices provide the foundation for creating immersive and engaging digital experiences.
Moreover, devices facilitate data exchange between users and applications, enabling real-time interactions and personalized content delivery. Whether a smartphone displays breaking news updates or a smartwatch tracks health data, devices seamlessly integrate data into our daily lives, making the digital experience more immersive and relevant.
Enhancing Software Usability through Devices
One of the key contributions of devices to the digital experience is the enhancement of software usability. Different devices offer unique interfaces and form factors, necessitating the adaptation of software to cater to varied user needs. For instance, a mobile app must be optimized for smaller screens and touch-based interactions, while a desktop application can leverage larger displays and traditional input methods.
By tailoring software interfaces to specific devices, businesses can create a seamless user experience that aligns with stakeholder preferences and usage patterns. This adaptability ensures users can effortlessly navigate and interact with digital content, leading to higher engagement and satisfaction.
The Impact of Devices on Data Access
The success of a digital experience heavily depends on the ease and speed with which stakeholders can access relevant data. Devices are critical in data accessibility, influencing how users interact with information and perform tasks. With their constant connectivity and portability, mobile devices have revolutionized how users access real-time data, enabling them to stay informed and make timely decisions.
Furthermore, the rise of cloud computing has further amplified the role of devices in data access. With cloud-based applications and services, stakeholders can seamlessly access and share data across multiple devices and locations. This flexibility empowers businesses to adopt agile practices and accommodate remote workforces, enhancing the digital experience.
Diverse User Experiences Across Devices
Different devices offer distinct user experiences influenced by screen size, mobility, and processing power. Stakeholder interactions and overall digital experiences vary across devices, from mobile devices catering to on-the-go users to desktops with comprehensive functionalities. Understanding these differences allows businesses to optimize their digital offerings and cater to diverse user needs.
Mobile Devices: On-The-Go Convenience
Mobile devices, particularly smartphones, have become integral to modern life. Their ubiquity and portability make them the go-to device for users seeking immediate access to information and services while on the move. The rise of mobile apps has further augmented the mobile experience, providing users with dedicated applications tailored to their needs.
Mobile devices present a unique opportunity for businesses to engage with stakeholders in real time. Mobile apps and responsive websites enable seamless interactions, offering personalized content, location-based services, and push notifications. By capitalizing on the mobile experience, businesses can cultivate stronger connections with their audience and drive brand loyalty.
Desktops: Comprehensive Functionality
In contrast to mobile devices, desktops provide larger screens and more robust processing capabilities, offering users a comprehensive digital experience. Desktop computers remain the preferred choice for tasks that require significant processing power, such as graphic design, video editing, and software development.
The desktop environment is well-suited for multi-tasking and productivity-oriented activities, allowing users to have multiple windows and applications open simultaneously. For businesses targeting professionals and power users, optimizing digital experiences for desktops is essential to meet their complex needs and ensure seamless workflows.
Tablets: Versatility and Portability
Tablets occupy a middle ground between smartphones and desktops, offering a balance of mobility and functionality. With larger screens than smartphones, tablets provide a more immersive experience for reading, multimedia consumption, and creative work.
Tablets’ versatility makes them popular in various industries, from healthcare and education to retail and hospitality. Their portability and touch-based interfaces offer stakeholders a convenient way to interact with digital content while on the move. Businesses can leverage tablets to create interactive presentations, offer digital menus, and facilitate seamless customer interactions.
Smartwatches and Wearables: Intuitive Accessibility
Smartwatches and wearable devices represent the next frontier in the digital experience landscape. These compact and intuitive gadgets provide quick access to essential information and health-related data. From receiving notifications and tracking fitness metrics to making contactless payments, wearables offer a seamless and hands-free digital experience.
For businesses, wearables present a novel opportunity to engage with stakeholders in novel and contextually relevant ways. By developing apps and services tailored to wearables, businesses can deliver personalized experiences that complement users’ daily activities, fostering stronger connections and brand loyalty.
Matching Devices to Stakeholder Needs
Tailoring device selection to match stakeholder needs is crucial in crafting exceptional digital experiences. Whether it’s sales representatives in the field or external partners, providing the right devices for accessing relevant data enhances productivity and fosters seamless interactions. This section emphasizes the importance of aligning devices with stakeholder tasks to create a harmonious digital ecosystem.
Understanding Stakeholder Personas
Before embarking on the journey of optimizing digital experiences, businesses must gain a comprehensive understanding of their stakeholders’ personas. A stakeholder persona encompasses various aspects such as demographics, preferences, pain points, and motivations. Creating detailed stakeholder personas allows businesses to empathize with their users, identify their needs, and align device selection with their expectations.
For example, a sales representative who spends most of their time on the road would benefit from a powerful and mobile-friendly device to access sales data and customer information on the go. Conversely, an executive responsible for strategic decision-making might require a larger, more robust device to analyze complex data sets and generate reports.
The Role of Data in Device Selection
Data plays a pivotal role in determining the appropriate devices for stakeholders. Understanding the types of data stakeholders need to access and the context in which they require it informs device selection. Businesses must prioritize data security and privacy concerns, especially when dealing with sensitive information.
By integrating data analytics and insights into device selection processes, businesses can fine-tune their digital experiences, ensuring stakeholders can access the right data at the right time. The seamless data flow across devices enhances stakeholder productivity, streamlines decision-making, and fosters a positive user experience.
Catering to Stakeholder Mobility Needs
The mobility requirements of stakeholders significantly influence device selection. Stakeholders working predominantly in office settings might benefit from desktops or laptops with larger screens and ergonomic keyboards. On the other hand, stakeholders who frequently travel or work remotely would require portable devices like smartphones, tablets, or lightweight laptops.
Moreover, businesses should explore the potential of cross-device compatibility, allowing stakeholders to seamlessly transition between devices without losing their progress or data. This continuity enhances the overall user experience and contributes to stakeholder satisfaction.
Accessibility and Inclusivity
Inclusive design is essential to device selection, ensuring that digital experiences cater to all stakeholders, regardless of their abilities or disabilities. Businesses should consider accessibility features such as screen readers, voice assistants, and adjustable font sizes to create a user-friendly experience for all users.
Accessibility measures not only enhance the digital experience for stakeholders with disabilities but also improve the overall usability for all users. It fosters a more inclusive and equitable digital environment, positively reflecting the organization’s brand image and reputation.
Securing Devices for Data Integrity
Ensuring robust security measures on devices is paramount for safeguarding company information and maintaining data integrity. This section delves into the significance of proper device security and its profound impact on the digital experience. Implementing effective device security strategies is crucial for a secure and seamless digital journey, from password protection to mitigating potential threats.
The Growing Importance of Device Security
In today’s interconnected world, where data breaches and cyber-attacks are increasingly common, securing devices is no longer an option but a necessity. Devices often store sensitive business data, user information, and proprietary software. Failure to implement robust security measures can lead to disastrous consequences, including data breaches, financial losses, and reputational damage.
Device security encompasses various layers of protection, including physical security, encryption, biometric authentication, and secure boot mechanisms. By adopting a multi-layered approach to device security, businesses can effectively safeguard their digital assets and fortify their digital experiences against potential threats.
Password Protection: The First Line of Defense
Passwords are the most common form of authentication for device access, making them the first defense against unauthorized access. This section delves into best practices for enforcing strong password policies, including complexity requirements, password expiration, and lockout parameters.
However, the challenge lies in promoting user compliance with password policies. Many users choose weak passwords or reuse passwords across multiple services, leaving devices vulnerable to hacking attempts. Businesses must educate stakeholders about the importance of password hygiene and consider implementing additional authentication methods, such as two-factor authentication (2FA), to bolster security.
Biometric Authentication: Embracing Convenience and Security
Biometric authentication, such as fingerprint scanning, facial recognition, and iris scanning, has gained popularity for its convenience and enhanced security. Biometrics provide a more secure alternative to traditional passwords, as they are difficult to replicate or share.
For businesses, biometric authentication can significantly improve the overall user experience by streamlining the login process. Stakeholders can securely access their devices with a simple fingerprint or facial scan, eliminating the need to remember complex passwords.
However, businesses must address privacy and data protection concerns when implementing biometric authentication. Clear communication about data usage and obtaining explicit user consent are essential for building trust and maintaining transparency.
Secure Boot and Firmware Integrity
During startup, secure boot mechanisms are essential for verifying the integrity of the device’s firmware and operating system. Secure boot ensures that only trusted software and firmware are loaded, reducing the risk of unauthorized modifications or malware infections.
By leveraging secure boot mechanisms, businesses can prevent attackers from exploiting vulnerabilities in the device’s boot process and ensure that the device starts in a trusted state. This level of security helps maintain data integrity and gives stakeholders the confidence that their data is protected from tampering.
Protecting Against Data Theft and Loss
Beyond securing the device itself, businesses must also address data protection in case of theft or loss of devices. Remote wipe capabilities enable businesses to erase sensitive data from lost or stolen devices, preventing unauthorized access to valuable information.
Moreover, businesses should encourage stakeholders to back up their data regularly to secure cloud storage or other devices. This practice ensures that critical data remains accessible even if the primary device is lost or damaged.
Guarding Devices Against External Threats
Devices are susceptible to external threats through Wi-Fi, Bluetooth, and other connectivity options. This section highlights the risks associated with external connections and their potential impact on data security. Effective measures against unauthorized access and malicious activities are essential for maintaining a secure digital experience.
The Risks of External Connections
While devices’ connectivity options, such as Wi-Fi and Bluetooth, enhance their usability, they expose devices to external threats. Hackers can exploit vulnerabilities in wireless connections to gain unauthorized access to devices and infiltrate the organization’s network.
Businesses should proactively mitigate these risks by implementing strong encryption protocols, regularly updating device firmware and software, and monitoring network traffic for suspicious activities.
Wi-Fi Security: Protecting Data in Transit
Wi-Fi networks are a common target for hackers seeking to intercept data transmitted over the air. This section explores the importance of securing Wi-Fi connections to safeguard sensitive data from eavesdropping and unauthorized access.
Wi-Fi encryption protocols such as WPA2 or WPA3 ensure that data transmitted between the device and the network remains encrypted, making it challenging for attackers to intercept and decipher. Additionally, businesses should avoid using open or unsecured Wi-Fi networks, especially when dealing with sensitive information.
Bluetooth Security: Securing Short-Range Communications
Bluetooth enables devices to connect wirelessly over short distances, making it a popular choice for various applications, such as wireless audio streaming and file sharing. However, Bluetooth’s convenience also presents security risks, as attackers can exploit vulnerabilities to gain unauthorized access to paired devices.
To enhance Bluetooth security, businesses should disable unnecessary Bluetooth services, enforce device pairing authentication, and ensure that devices have the latest firmware updates to address known security flaws.
Mitigating the Threat of Physical Access
Physical access to a device can harm data security, as attackers can compromise devices directly or insert malicious hardware like USB drives. This section examines strategies for preventing unauthorized physical access to devices and protecting data in case of device theft.
Businesses can deploy features like screen locking and password requirements after a period of inactivity to prevent unauthorized access. Additionally, encrypting data stored on the device ensures that even if the device falls into the wrong hands, the data remains unreadable without the decryption key.
Data Accessibility and Stakeholder Empowerment
Data accessibility is at the core of a seamless digital experience for stakeholders. This section explores how data connectivity and device selection influence stakeholder engagement with software interfaces. Ensuring uninterrupted access to real-time information empowers stakeholders to make informed decisions and enhances their overall experience.
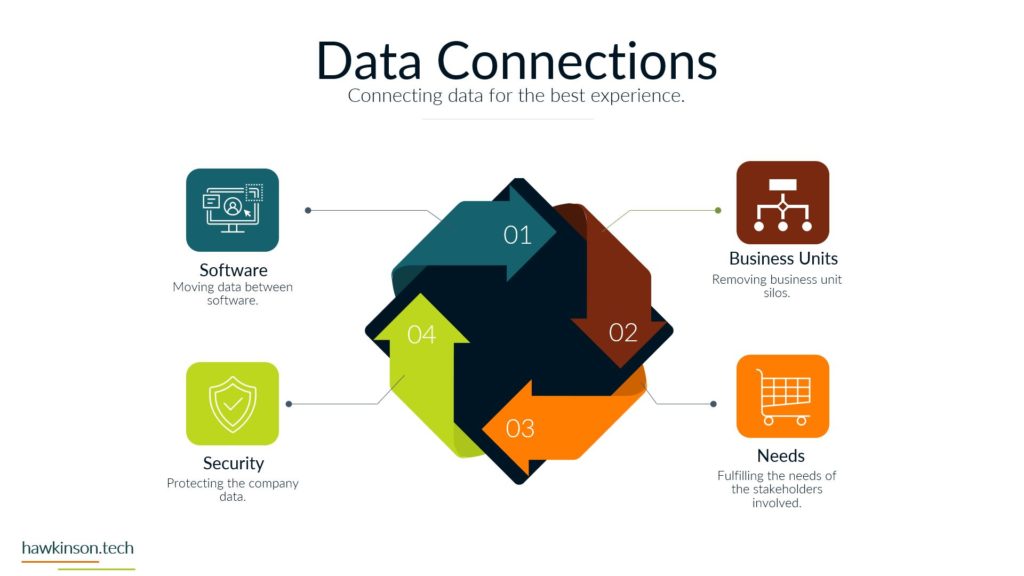
The Role of Data Connectivity
Data connectivity is critical in facilitating seamless stakeholder interactions with digital interfaces. Fast and reliable data connections ensure stakeholders can access real-time information and perform tasks efficiently.
For businesses operating in areas with limited network coverage, implementing data caching mechanisms allows stakeholders to access critical data offline, minimizing disruptions in productivity. Optimizing data delivery and reducing latency also contribute to a smoother and more responsive digital experience.
Balancing Data Privacy and Accessibility
While ensuring data accessibility is crucial, businesses must balance data privacy and security. This section delves into the importance of protecting sensitive information while providing stakeholders with the data they need to perform their tasks.
By anonymizing and aggregating data, businesses can provide valuable insights to stakeholders without compromising individual privacy. Compliance with data protection regulations, such as GDPR and CCPA, is vital in building trust and maintaining ethical data practices.
Real-Time Data Analytics for Stakeholder Insights
Real-time data analytics empowers stakeholders with valuable insights, enabling data-driven decision-making. This section explores the role of real-time data analytics in enhancing stakeholder engagement and providing personalized experiences.
By leveraging data analytics, businesses can identify patterns, trends, and customer behaviors, enabling them to tailor digital experiences to meet specific stakeholder needs. Moreover, real-time data analytics enables businesses to respond quickly to changing market conditions and make strategic decisions based on current information.
Enabling Collaboration Through Data Sharing
Data sharing among stakeholders fosters collaboration and enhances the overall digital experience. This section discusses the importance of facilitating data sharing and collaboration among stakeholders within and outside the organization.
Businesses can implement data-sharing platforms and tools that enable stakeholders to collaborate seamlessly, ensuring that all relevant parties can access the most up-to-date information. Collaboration platforms like shared project management tools and document repositories streamline workflows and boost stakeholder productivity.
Personalizing Data Access for Stakeholder Needs
Different stakeholders have diverse data requirements, and personalized data access is pivotal for optimizing the digital experience. This section delves into the importance of tailoring data accessibility to match individual stakeholder needs and tasks. A personalized approach fosters deeper stakeholder engagement and increases overall satisfaction.
Customizing Data Dashboards and Reports
Providing stakeholders with customizable data dashboards and reports enables them to access the information most relevant to their roles and responsibilities. This section discusses the benefits of tailoring data presentation to match stakeholder preferences and requirements.
Customizable dashboards and reports empower stakeholders to create personalized data views, facilitating faster and more informed decision-making. Businesses can leverage user feedback and analytics to continuously improve data visualizations and ensure stakeholders have a seamless and productive experience.
Contextual Data Recommendations
Contextual data recommendations offer stakeholders relevant insights based on their current tasks and interactions. By leveraging artificial intelligence and machine learning algorithms, businesses can analyze stakeholder behavior and deliver data recommendations that align with their needs.
Contextual data recommendations enhance stakeholder productivity by presenting relevant information at the right time, reducing the need for manual data exploration and search. This personalization approach contributes to stakeholder satisfaction and reinforces the value of the digital experience.
Data Access Control and Permissions
Implementing granular data access control and permissions is essential for ensuring data security and privacy while enabling personalized data access. This section explores the importance of role-based access and user permissions to safeguard sensitive information.
Businesses can implement access control mechanisms that restrict data access to authorized stakeholders, preventing unauthorized users from accessing confidential information. Role-based access ensures that stakeholders can only access the data relevant to their roles, reducing the risk of data breaches and unauthorized data sharing.
User Feedback and Continuous Improvement
Gathering user feedback and insights is critical for continuously improving the digital experience. This section emphasizes the significance of soliciting stakeholder feedback to identify pain points and opportunities for optimization.
Feedback from stakeholders allows businesses to address usability issues, identify feature requests, and prioritize enhancements that align with stakeholder needs. By iterating and refining the digital experience based on user feedback, businesses can create a truly customer-centric environment that fosters stakeholder loyalty and engagement.
Harmonizing Devices and Data for Enhanced Digital Experiences
As we conclude this article on the impact of devices on digital experiences, we recognize their pivotal role in shaping interactions, data accessibility, and overall security. Harmonizing data and devices in a business environment empowers stakeholders to navigate the digital landscape seamlessly and effectively. By aligning device selection with stakeholder needs and prioritizing data security, businesses can deliver exceptional digital experiences that drive growth, productivity, and customer satisfaction. Stay tuned for more insights into the dynamic duo of data and devices in digital experiences. Together, they hold the key to unlocking unparalleled possibilities in the digital realm, propelling businesses toward success in an increasingly interconnected and data-driven world.